Ethical Hacking Course in Marathahalli
Get EC council certified in just 6 weeks, Become an ethical hacker or cyber security expert.
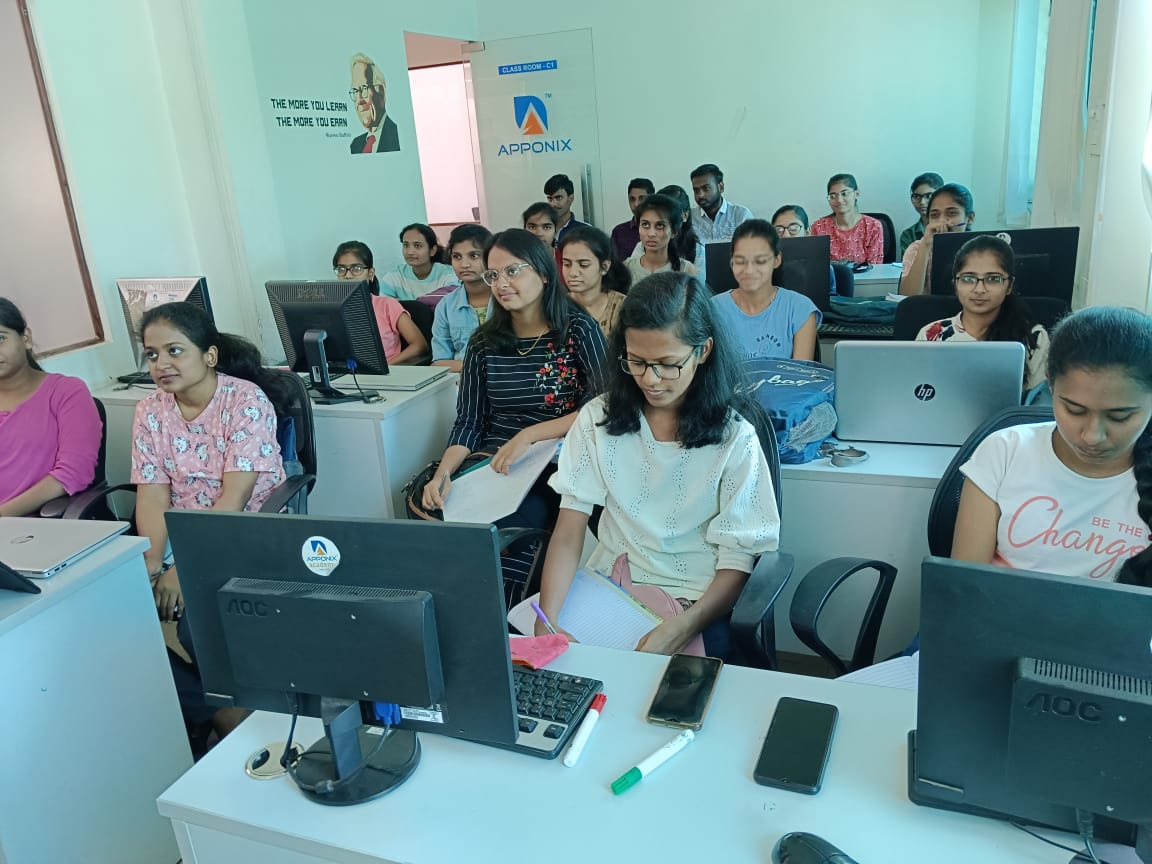
At Apponix, we offer our ethical hacking course in Marathahalli through a hands-on learning approach that helps you understand security tools, attack methods, and defense techniques with complete clarity. We make every session practical and beginner-friendly.
Because Marathahalli is one of our major Bangalore training hubs, this program aligns with our larger ethical hacking course in Bangalore, giving you the same expert trainers, engaging labs, and interactive guidance throughout your learning journey.
We also support you with certification preparation, skill-building exercises, and placement assistance so you feel confident taking the next step toward a successful cybersecurity career.
2000+ Ratings
3000+ Happy Learners
Ethical Hacking Videos
Skills Covered in Ethical Hacking Course
Course Key Features
Our Alumni Working in




































Ethical Hacking Course Reviews
I did ethical hacking training from Apponix. It was a wonderful experience. The trainer helped me to understand hacking technologies and the tools.
Great infrastructure. The faculty and staffs are friendly. The tutor is very much approachable. His teaching style is very nice.
The training was totally amazing. It really saved my career. A super trainer who is a real expert. Great infrastructure. The faculty and staffs are friendly.
Our Recent Placements
Why is Apponix’s Ethical Hacking Training Course the Best?
- Apponix Academy offers expert-led training focused on practical learning, allowing students to master essential ethical hacking tools with real-world insights.
- The course includes structured labs, guided sessions, and support that builds strong confidence for tackling cybersecurity challenges professionally.
- Students receive soft skills coaching, interview preparation, and placement assistance, helping them transition smoothly into cybersecurity roles.
- Apponix provides flexible learning options, ensuring every learner progresses comfortably through comprehensive, industry-relevant ethical hacking training modules.
Why Do Students Choose Apponix for an Ethical Hacking Course in Marathahalli?
- We offer practical, tool-based ethical hacking training guided by experienced mentors who focus on building real security skills through structured, hands-on practice.
- Our Marathahalli centre provides supportive learning environments with flexible online and classroom batches suitable for beginners and working professionals seeking cybersecurity careers.
- We include resume building, interview preparation, and dedicated placement assistance designed to help students secure strong job opportunities in top companies.
- Students trust our consistent training quality across Bangalore locations, ensuring expert-driven modules, interactive labs, and personalised mentorship for complete ethical hacking career readiness.
Classroom Training
Classroom Training







Fees & Training Options
Online Training
- Interactive Live Training Sessions
- 40+ Hrs Practical Learning
- Delivered by Working Professionals
- 1-Year Access to Recorded Sessions
- Placement assistance will be provided
- Guaranteed 3 Interview Arrangements
- Daily 2 Hrs or Weekend 10 Hrs
- EC-Council Certification Assistance
- Doubt Clearing Sessions
- Regular assignments will be given and assessments will be taken.
Ethical Hacking Training Syllabus
Prerequisites
This course can be taken by any one who is interested in learning hacking or who wants to start their career in ethical hacking.
Below IT professionals also can take this course to further enhance their career opportunities.
- Network security officers
- Website administrators
- IS/IT specialists
- IS/IT analysts
- IS/IT auditors
- IT operations managers
- IT security officers
- Network specialists
- Technical support engineers
- Senior systems engineers and
- Systems analysts.
Ethical Hacking Course Syllabus
1 Demo of Aspen and iLabs
2 Internet is Integral Part of Business and Personal Life - What Happens Online in 60 Seconds
3 Essential Terminology
4 Elements of Information Security
5 The Security, Functionality, and Usability Triangle
1 Motives, Goals, and Objectives of Information Security Attacks
2 Top Information Security Attack Vectors
3 Information Security Threat Categories
4 Types of Attacks on a System
5 Information Warfare
1 What is Hacking
2 Who is a Hacker?
3 Hacker Classes
4 Hacking Phases
1 What is Ethical Hacking?
2 Why Ethical Hacking is Necessary
3 Scope and Limitations of Ethical Hacking
4 Skills of an Ethical Hacker
1 Information Assurance (IA)
2 Information Security Management Program
4 Enterprise Information Security Architecture (EISA)
5 Network Security Zoning
6 Defense in Depth
7 Information Security Policies
8 Physical Security
10 What is Risk?
11 Threat Modeling
12 Incident Management
13 Security Incident and Event Management (SIEM)
14 User Behavior Analytics (UBA)
15 Network Security Controls
16 Identity and Access Management (IAM)
17 Data Leakage
18 Data Backup
19 Data Recovery
20 Role of AI/ML in Cyber Securit
1 Penetration Testing
2 Why Penetration Testing
3 Comparing Security Audit, Vulnerability Assessment, and Penetration Testing
4 Blue Teaming/Red Teaming
5 Types of Penetration Testing
6 Phases of Penetration Testing
7 Security Testing Methodology
1 Payment Card Industry Data Security Standard (PCI-DSS)
2 ISO/IEC 27001:2013
3 Health Insurance Portability and Accountability Act (HIPAA)
4 Sarbanes Oxley Act (SOX)
5 The Digital Millennium Copyright Act (DMCA)
6 Federal Information Security Management Act (FISMA)
7 Cyber Law in Different Countries
1 What is Footprinting?
2 Objectives of Footprinting
1 Footprinting through Search Engines
2 Footprinting using Advanced Google Hacking Techniques
3 Information Gathering Using Google Advanced Search and Image Search
4 Google Hacking Database
5 VoIP and VPN Footprinting through Google Hacking Database
1 Finding Company’s Top-level Domains (TLDs) and Sub-domains
2 Finding the Geographical Location of the Target
3 People Search on Social Networking Sites and People Search Service
4 Gathering Information from LinkedIn
5 Gather Information from Financial Services
6 Footprinting through Job Sites
7 Monitoring Target Using Alerts
8 Information Gathering Using Groups, Forums, and Blogs
9 Determining the Operating System
10 VoIP and VPN Footprinting through SHODAN
1 Collecting Information through Social Engineering on Social Networking Sites
1 Website Footprinting
2 Website Footprinting using Web Spiders
3 Mirroring Entire Website
4 Extracting Website Information from https://archive.org
5 Extracting Metadata of Public Documents
6 Monitoring Web Pages for Updates and Changes
1 Tracking Email Communications
2 Collecting Information from Email Header
3 Email Tracking Tools
1 Competitive Intelligence Gathering
2 Competitive Intelligence - When Did this Company Begin? How Did it Develop?
3 Competitive Intelligence - What Are the Company's Plans?
4 Competitive Intelligence - What Expert Opinions Say About the Company
5 Monitoring Website Traffic of Target Company
6 Tracking Online Reputation of the Target
1 Whois Lookup
2 Whois Lookup Result Analysis
3 Whois Lookup Tools
4 Finding IP Geolocation Information
1 Extracting DNS Information
2 DNS Interrogation Tools
1 Locate the Network Range
2 Traceroute
3 Traceroute
4 Traceroute Tools
1 Footprinting through Social Engineering
2 Collect Information Using Eavesdropping, Shoulder Surfing, and Dumpster Diving
1 Maltego
2 Recon-ng
3 FOCA
4 Recon-Dog
5 OSRFramework
6 Additional Footprinting Tools
1 Footprinting Countermeasures
1 Footprinting Pen Testing
2 Footprinting Pen Testing Report Templates
1 Overview of Network Scanning
2 TCP Communication Flags
3 TCP/IP Communication
4 Creating Custom Packet Using TCP Flags
5 Scanning in IPv6 Networks
1 Nmap
2 Hping2 / Hping3
3 Scanning Tools
4 Scanning Tools for Mobile
1 Scanning Technique
2 Port Scanning Countermeasures
1 IDS/Firewall Evasion Techniques
1 Banner Grabbing
2 How to Identify Target System OS
03:063 Banner Grabbing Countermeasures
1 Draw Network Diagrams
2 Network Discovery and Mapping Tools
3 Network Discovery Tools for Mobile
1 Scanning Pen Testing
1 What is Enumeration?
2 Techniques for Enumeration
3 Services and Ports to Enumerate
1 NetBIOS Enumeration
2 NetBIOS Enumeration Tool
3 Enumerating User Accounts
4 Enumerating Shared Resources Using Net View
1 SNMP (Simple Network Management Protocol) Enumeration
2 Working of SNMP
3 Management Information Base (MIB)
4 SNMP Enumeration Tools
1 LDAP Enumeration
2 LDAP Enumeration Tools
1 NTP Enumeration
2 NTP Enumeration Commands
2 NTP Enumeration Tools
1 SMTP Enumeration
2 SMTP Enumeration Tools
3 DNS Enumeration Using Zone Transfer
1 IPsec Enumeration
2 VoIP Enumeration
3 RPC Enumeration
4 Unix/Linux User Enumeration
1 Enumeration Countermeasures
1 Enumeration Pen Testing
+91 80505-80888
Our Top Instructors
Overview of Ethical Hacking Course in Marathahalli
- We offer practical ethical hacking training focused on real-world tools, interactive labs, and guided mentorship to help you build strong security skills confidently.
- Our Marathahalli program includes in-depth modules covering network attacks, system vulnerabilities, web application security, and cybersecurity fundamentals essential for modern IT careers.
- We train you using hands-on scenarios that simulate actual cyber threats, helping you understand attacker techniques and effective defensive strategies through structured learning.
- Our sessions are led by experienced security professionals who bring industry knowledge, mentorship, and clarity to every complex ethical hacking concept taught.
- We provide a supportive learning environment with flexible batches, practical assignments, and placement assistance to help you transition smoothly into cybersecurity roles.
Benefits of an Ethical Hacking Course
- Learn to identify vulnerabilities in systems and networks using structured methodologies, practical tools, and real-world ethical hacking techniques effectively.
- Develop strong problem-solving skills by understanding attacker mindsets, security loopholes, and defensive strategies essential for modern cybersecurity roles.
- Gain hands-on experience with industry tools that enhance your technical confidence and prepare you for security assessments in professional environments.
- Improve your career prospects by acquiring specialized skills that are highly valued across IT companies, security teams, and growing tech industries today.
- Build a strong foundation in cybersecurity concepts while learning responsible practices that help protect digital assets, users, and organizational systems efficiently.
Related job roles
- Ethical Hacker
- Information Security Analyst
- Security Analyst
- Certified Ethical Hacker (CEH)
- Security Consultant
- Information Security Manager
- Penetration Tester
Ethical Hacking Training
Program Highlights
- Certified & Experienced Trainers
- Lab-Based Practical Sessions
- Full Placement Assistance
- Weekend and Online Batches Available
- Real-World Cybersecurity Projects
Is it legal to take this course?
Yes, ethical hacking is legal and it is also legal to learn the practice of ethical hacking.
The tools used in the white hat hacking will be similar to black-hat hacking but since you will be certified, you will always be working from the right side of the law.
Will I get a job after taking this course?
Yes, companies from all sectors of the economy need the services of ethical hackers to keep the IT infrastructure safe. Hence, whether you want to get a job in India or abroad, your chances of getting employed will be high – especially when compared to non-certified ethical hackers.

Ethical Hacking Training
Who will take the classes?
All of our highly qualified trainers with at least 7+ years of experience in ethical hacking and working in the areas of cybersecurity and IT service and architecture.
Each of them has gone through a good selection process that includes profile screening, technical evaluation, and a training demo before they are certified to train for us.
We also ensure that only those trainers with a high alumni rating remain on our faculty.
Why take this course?
You need to take this course if you want to have an exciting career in IT.
Compared to software development and web development, the challenges that come with ethical hacking will always leave you wanting more.
A career in ethical hacking will not be a boring one and the best part, you will be paid well too!